How Identity and Access Management Helps CISOs and CIOs?
There are certain struggles and strategies that CISOs and CIOs have to make…
… to prevent their system from malicious threats, and provide a smooth user experience to the users.
That is where IAM comes to the rescue.
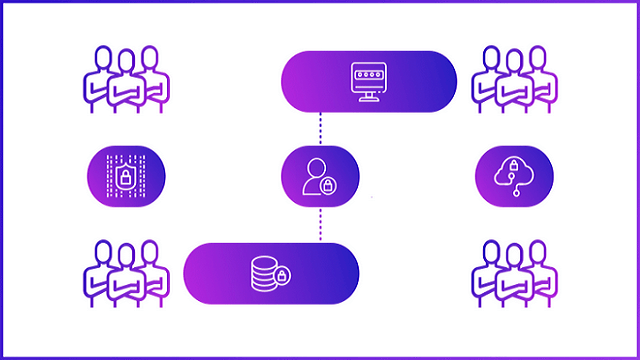
Identity and Access Management deals with defining & managing security roles for providing access privileges to employees and users to handle organization resources.
It provides robust security with a better user experience and relieves security officers from unnecessary worry.
In this blog, let’s discuss how Identity and Access Management (IAM) solution helps CISOs and CIOs to overcome various problems related to cyber-security.
Challenges That CISOs and CIOs Face:
There are various security challenges that CISOs and CIOs face while setting up or configuring the entire security framework and infrastructure for an organization.
Here is a list of challenges that CISOs and CIOs tackle for better security edges.
#1. Industry Standard Compliances and Privacy Related Issues:
With the rise of security breaches and privacy threats, organizations get strict regulations to adhere to the data security and privacy compliances that align with the industry standards.
All the data storage, transactions, and other operations related to user data have to be according to the user’s consent.
Privacy breaches because of not adhering to proper industry compliances can lead to the loss of an organization’s revenue and can even damage an organization’s reputation.
CISOs and CIOs can implement IAM solutions that come with various compliances like GDPR, HIPAA, COPPA, etc., so that the security officers and top executive leaders do not have to keep a check on the compliance updates and adherence.
#2. Authenticate Employees From Anywhere to Anything:
Accessing employees apart from their organization premises has now gone with the advent of work from home culture.
The pandemic gave a challenge to the CISOs and CIOs, as organization security officers have to decide how to manage organization resource security, yet provide access to employees who are working from their homes or other remote places.
Therefore, to bridge the gap, CISOs have started implementing Identity & Access Management (IAM) solutions which make remote authentication very easy.
It brings in the concept of “Bring your own identity (BYOID),” which allows employees and IAM users to bring their own identities and enable federated identity culture.
IAMs use Single Sign-On (SSO) that promotes federated identity and easy access to various resources.
#3. Challenges With User Experience (UX):
Registration pages, login screens, and authentication interfaces are the most interactive pages that appear every time.
Often such screens become the gateway to the application & keeping it interactive or visually appealing is essential.
IAMs and CIAMs can help solve the issue.
Also, IAMs allow identity federation by allowing access through multiple accounts of different apps and services through one single login token seamlessly.
Facilities like a simple registration process, easy password resetting technique, link-based login alternatives, simple user interface, and meaningful error messages are some traits that make IAM the best choice for CISOs and CIOs.
#4. Increase Productivity Without Compromising Security:
Often security systems try to become more easy-going to increase user experience and productivity.
But this often loses emphasis on the security part of the apps.
Again, security breaches become higher when employees need to log in to multiple services through various identity providers.
CISOs and CIOs need to cover all the issues, yet render productivity without making security and authentication the barrier.
IAMs allow social login, phone login, QR code login, magic links, and OTP-based login methods that can authenticate valid users in one go.
Also, Single Sign-On (SSO) promotes federated identity, making authentication seamless without losing employees’ productivity.
All these various authentication techniques make IAM products more suitable for organization security with productivity & helps CISOs and CIOs provide a better security framework.
#5. Provide Enhanced Security With Dynamic and Intelligent Measures:
The art of exploiting security vulnerabilities has become complicated with the rise of technological advancement.
In the fast-paced world, businesses should be agile.
So, businesses use multiple frameworks, APIs, and tools to bring development and operational productivity.
This may also bring threats to the organization.
Therefore, to stay vigilant, CISOs and CIOs prefer to use IAM solutions because these security solutions come with AI and ML to understand threat behavior and check for signatures dynamically.
Modern IAMs also come with risk-based authentication and understand employee login patterns to provide additional implicit security.
Also, security officers prefer IAM because it can monitor and detect internal threats or even predict them before happening.
#6. 24 X 7 Security Support:
At times, it becomes hectic for CISOs and CIOs to be on call 24×7 for taking care of organization security.
Threat actors do not sleep or take holidays and try different attack techniques to make the life of cyber security officers difficult.
It often spoils the personal life of a cyber security officer.
But with the advent of Identity and Access Management, together with Intrusion Detection System (IDS) and Intrusion Prevention System (IPS), continuous monitoring and threat alert techniques…
… CISOs and CIOs do not have to worry about security threats all the time or take up phone calls 24×7.
With IAM, it becomes easy to notify IT officers or security professionals about cyber threats during emergency situations.
Conclusion:
We hope this blog has given a crisp idea about the various aspects and justifications about how IAM can help CISOs and CIOs to enable better security in the organizations.
We cannot deny the fact that IAM turns out to be an all-in-one framework for organization security.
It helps to provide strategic ways to secure the organization from internal and external threats.
Secure your organization right now – Start 15 Days Free Trial